Early this morning a Facebook acquaintance, henceforth known as “S,” reached out to me with an interesting problem. Some time ago, she bought a laptop from a liquidation auction at Living Social. When she finally got around to booting it up, she discovered something concerning. What follows is our conversation:
S: Hey there! have a tech question for you….I bought a laptop from an auction at Living Social a couple of months ago. Said laptop was supposed to have been wiped clean, but it wasn’t (requires the former users password). Tried calling/emailing Living social, but they’ve been completely non responsive. How can I reboot it?
Mrs. Y: …that’s quite frightening, that someone’s personal data is on a laptop that was resold. I can try reaching out to contacts at Living Social, but probably won’t get you much. Was it supposed to come with an operating system already installed?
S: When it boots up it MS7 Enterprise. It’s not supposed to come with an operating system.
Mrs. Y: Yikes. Okay, I would just reinstall, unless you want me to break into it and figure out which organization or individual was silly enough to give an unwiped laptop over to an auction. If it’s MS 7 enterprise, I’m betting that it was an organization and it might have confidential data on it. FYI this is every security professional’s nightmare
S: it was Living Social. They were liquidating from their 9th street office. That’s why I tried reaching out to them. Thought it made sense to let them know and I could bring it back to them so they could wipe it.
Mrs. Y: (Where I finally realize that the laptop formerly BELONGED to Living Social, not simply being resold by them.) holy crap!
hahahhahhaha
OMG
that’s friggin’ hysterical
Mrs. Y: You are so honest. Most would have already broken into it. I can reach out to contacts, but you can probably wipe. I mean, that’s probably the safest thing for you to do. Honestly, they probably won’t have time to deal with it or care since they’re downsizing. They won’t have the staff to deal with it. Worst part is that it doesn’t seem to be encrypted.
S: If you want to break into it, I’m fine with that! I feel I did my due diligence in alerting them.
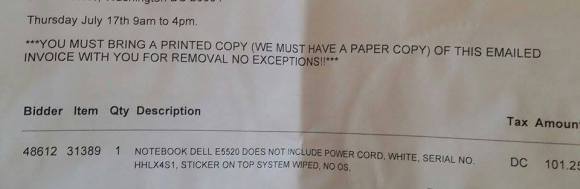
Mrs. Y: (Yielding to my better nature) I reached out to them via Twitter. BTW, is there anything that identifies the system as previously having belonged to Living Social? An asset tag or branding when the OS boots up? Feel free to send me screenshots.


Reblogged this on oogenhand.